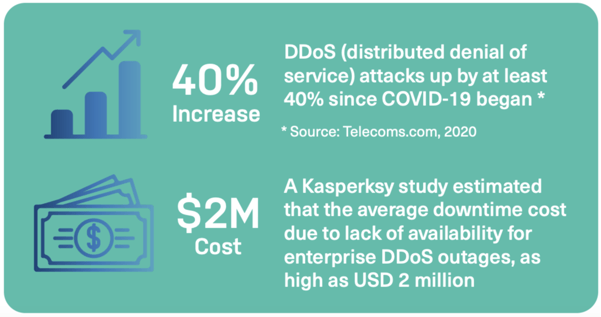
While new cybersecurity threats emerge all the time, some long-standing basic threats have never gone away. The humble brute-force security attack, the distributed denial of service (DDoS), came back with a vengeance during the COVID crisis. Amazon experienced the largest DDoS attack of all time in February 2020, and there were large attacks on gaming and media sites and servers, as well as an onslaught of ransom-driven DDoS attacks.
Alongside surging frequency, the basic DDoS attack has grown more diverse and destructive, particularly during this period of increased vulnerability.
Re-evaluating the standard DDoS threat
DDoS attacks have always been about using sheer brute force to overwhelm existing resources and keep website traffic from moving. During the coronavirus crisis, organizations globally have moved en masse to online operations, and the world has leapt at least a decade forward in terms of digital transformation efforts. E-commerce has boomed; learning and working from home have become the norm, and this period of adjustment has been accompanied by unprecedented levels of web traffic. In this changing landscape, some of this traffic is legitimate, but a lot of it is the result of DDoS attacks, a cybersecurity phantom that has found in COVID a host for viral proliferation.
The bitter pill of unheeded warnings
Since the last time we discussed DDoS, the renaissance of DDoS has not waned. According to NETSCOUT’s ATLAS Security Engineering and Response Team, the number of DDoS attacks exceeded 10 million in 2020, which was 1.6 million more attacks than 2019.
The security firm Kaspersky has visualized the difference between 2019 and 2020, also pointing out that in normal years, the second half of the year (Q3) usually shows a marked drop in DDoS traffic, which definitely did not happen in 2020.
DDoS attack comparison by %, 2019/2020, Kaspersky
DDoS is not dying down. In fact, these attacks are growing bigger in scope and size, longer in duration, and worsened by amplification methods across multiple vectors, now with an added bonus: extortion. Threat actors have begun to target businesses with DDoS attacks, demand a random, and if the company doesn’t pay, they use this as justification to resume the barrage. These kinds of “payday DDoS” efforts concentrate focus on a mix of monied entities, such as financial institutions, and critical services, such as healthcare and pharmaceutical companies and ISPs and communications providers. Schools and universities have also been targeted by floods of disruptive useless traffic, as people continued learning from home.
At the same time, many DDoS attacks are diversionary tactics, meant to get security teams to take their eye off the ball, distracted by dealing with the attack while cybercriminals get on with their real malicious aims.
DDoS: A global pandemic
No region in the world is immune to the peril of DDoS attacks. Kaspersky statistics highlight the top DDoS victims: China, the United States and Hong Kong.
Distribution of unique DDoS-attack targets by country, Q3 and Q4 2020, Kaspersky
Defense by design
One of the most basic things enterprises can do is implement security-by-design strategies as a first defense layer. Detection is one of the most effective routes to prevention, and security layers and mitigation techniques ensure sufficient oversight in detecting and protecting potential cybersecurity issues, particularly DDoS attacks.
Standard security solutions: First line of defense
- DDoS detection (rate limiting, request inspection/throttling)
- cache poisoning mitigation strategies
- front and backend TLS
- web application firewall (WAF)
- total cache encryption (make stolen or leaked data useless)
Other mitigation techniques:
- origin shield (protect backend servers from DDoS or other traffic tsunamis; monitoring and shielding at the network edge)
- high availability setups
- customizable authorization/authentication policy for access control, customizable paywalls and single sign-on integrations
- real-time traffic monitoring (employed in DDoS prevention)
Vaccinating yourself against DDoS
As with actual vaccinations, nothing is 100% effective but there are clear mitigation tools, techniques and practices that can help you avoid the worst of what DDoS can do.


